IP address geolocation is one of the Internet's most relied-upon “coarse signals.” It answers a deceptively simple question — "where is this IP?" — and that answer influences everything from content localization and CDN steering to fraud detection, regulatory gating, and performance measurement.
Yet the ecosystem routinely fails in predictable ways: ranges are labeled too broadly, feeds go stale, leased space creates conflicting claims, discovery links break, and consumers struggle to verify whether a published location is authoritative. The result is costly friction: misrouted traffic, incorrect geo-blocks, false fraud alerts, and confused end users.
This blog post highlights the key ideas from IPGeolocation’s IETF-published position paper, "IP Address Geolocation – Use Cases, Gaps, and Future Directions," and translates them into actionable practices that networks, platforms, and geolocation consumers can implement immediately.
Why IP Geolocation matters: The core use cases

1. Content localization and Access control
Streaming platforms, publishers, and regulated services routinely tailor experiences by country/region—catalog availability, pricing, language defaults, and access constraints. When geolocation is wrong, users see unavailable content, receive incorrect redirects, or get blocked unnecessarily.
2. CDN mapping and Edge selection
CDNs and edge networks use IP geolocation to place users on nearby infrastructure to reduce latency. Gaming and realtime services also depend on region-appropriate matching and routing. Bad IP-geo means higher latency, inconsistent performance, and poor user experience.
3. Search, Ads, and Personalization
Search engines and ad systems use coarse location to return relevant results ("coffee shops", "events this weekend") and improve engagement with regional relevance. When the signal is inaccurate, the experience degrades immediately—and visibly.
4. Security and Fraud analytics
Risk engines use location anomalies (impossible travel, cross-border login changes, mismatches versus shipping/BIN/phone signals) for step-up authentication and fraud prevention. If IP-geo is wrong, legitimate users get challenged or blocked, while adversaries may slip through when anomalies are missed.
What's broken: The Failures are not random

The position paper identifies several recurring failure modes that explain the bulk of real-world "my IP is in the wrong city/country" incidents.
1. Data is too coarse to be useful
A common pattern is a single location applied to a very large range (especially in IPv6), even when the range spans multiple cities or regions. That may be "technically populated," but practically incorrect—and it creates avoidable harm in routing, fraud checks, and content decisions.
2. Conflicting or Duplicate entries (especially with leased space)
When an upstream network leases or delegates a sub-range, both parties sometimes publish geolocation for the same prefixes. Consumers then receive contradictory claims for identical CIDRs—undermining trust and producing inconsistent results across vendors and platforms.
3. Poor maintenance and Low coverage
Some feeds are never updated after initial publication, and others are not discoverable because the geofeed URL is missing from WHOIS/RDAP records. Even when URLs exist, broken links and server errors are common. Consumers cannot rely on data that is not retrievable and refreshed predictably.
4. Quality and Formatting issues
Malformed rows, duplicate CIDRs, typos in prefix length, invalid region/country codes, and parsing-breaking whitespace/encoding are all frequent. Many publishers lack validation tooling, so bad data ships and stays bad.
5. Trust and Privacy gaps
Any network can publish a claim, but consumers need a way to verify authority and integrity. Separately, pushing granularity too far can raise privacy concerns by enabling overly precise inference. Today's ecosystem lacks consistent, automated authenticity checks and a shared privacy governance approach.
The Path Forward: Practical Fixes that can work at Internet scale

The paper's core argument is not that IP geolocation will ever be perfect—it will remain an approximate signal. The goal is more realistic and more valuable: move the ecosystem from "Best-effort Guess" to a dependable coarse signal through implementable operational practices.
1. Use Geofeeds for faster, more accurate updates
A major opportunity is wider, higher-quality adoption of geofeeds: self-published mappings of IP prefixes to locations. When maintained and discoverable, geofeeds can update far faster than static, third-party databases—particularly during renumbering, reassignment, or network changes.
2. Improve timeliness with automation and explicit freshness
The paper recommends automating feed generation so updates occur immediately after allocation/lease/routing changes, publishing over stable HTTPS, and using cache headers to guide refresh cycles. A pragmatic freshness window is on the order of days, not months—especially for networks with frequent churn.
3. Raise data quality with "Fail-Closed" validation
Consumers should treat duplicate CIDRs, overlapping same-length entries with different locales, and non-standard codes as errors—not "last one wins." Publishers should validate ISO country codes and region/admin codes and eliminate malformed rows before publishing.
4. Coordinate lessor–lessee semantics (replace, don't append)
When address space is leased or delegated, the correct operational model is replace semantics: the lessee publishes the sub-prefix, and the lessor removes that exact sub-prefix from the parent feed so there is only one authoritative claim per prefix. This single change prevents a large fraction of the conflicts seen in the wild.
5. Strengthen authenticity (where feasible)
The paper calls out the need to authenticate geolocation at the source—e.g., via signing approaches tied to routing/authority mechanisms—so consumers can verify integrity and provenance rather than "trusting by default."
6. Consider alternatives that rely less on IP-derived location
For some use cases, IP is simply the wrong tool. Device-consented location, privacy-aware tokens that assert coarse region, and ISP-provided, rate-limited authoritative APIs can reduce dependence on inferred IP location—especially where precision and privacy are in tension.
An operator's checklist: Publish Geofeeds that consumers can trust
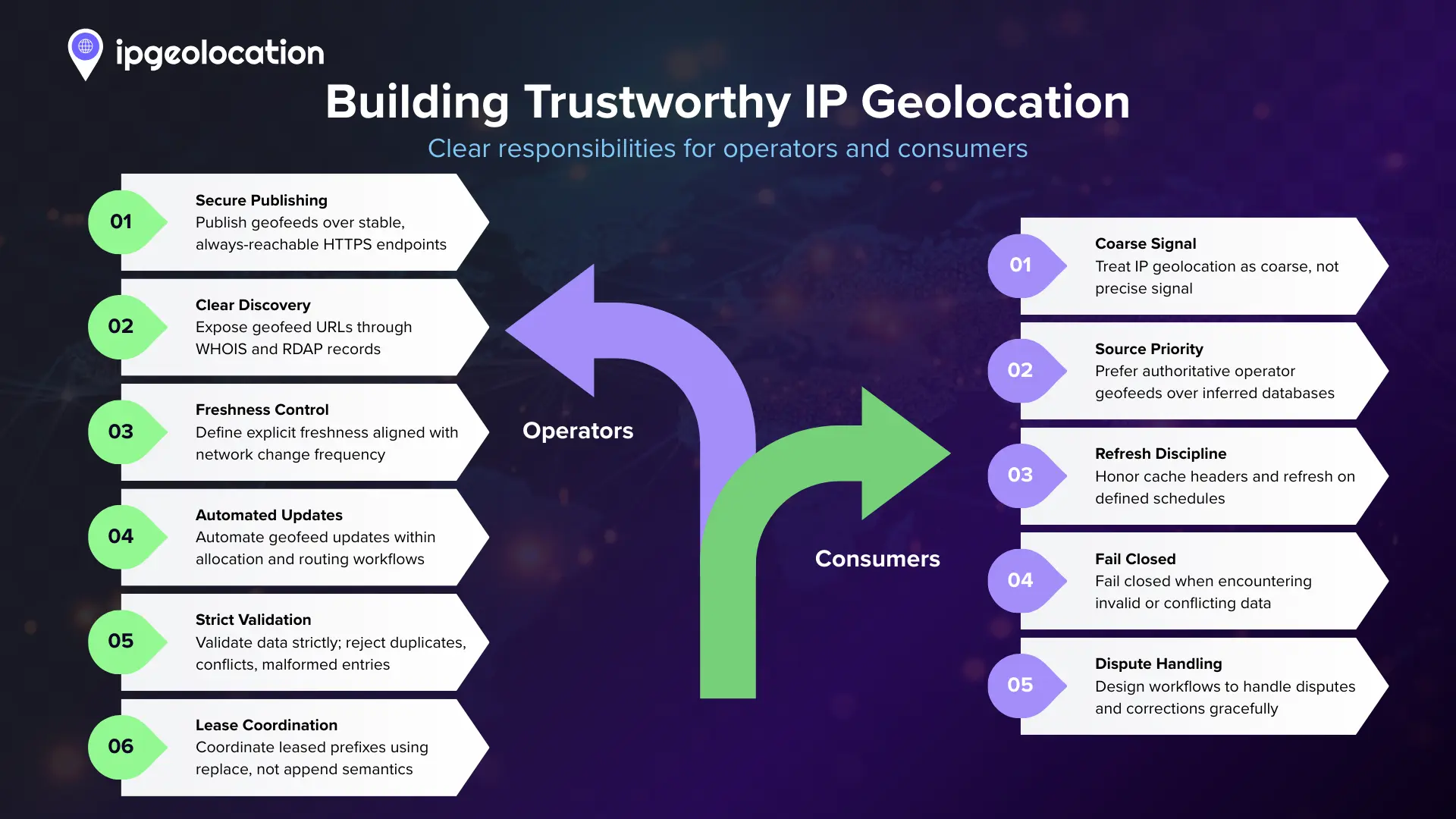
If you operate a network (or you manage IP space on behalf of one), these practices are implementable and immediately beneficial:
- Publish a geofeed on stable HTTPS and keep it reachable.
- Make it discoverable by placing the geofeed pointer in WHOIS/RDAP where supported.
- Set explicit freshness (cache-control max-age) aligned to your churn (commonly 1–7 days).
- Automate updates as part of allocation/lease/routing workflows—avoid manual edits.
- Validate before publishing: fail on duplicate CIDRs, malformed prefixes, non-standard codes, and conflicting overlaps.
- Coordinate leased space: remove sub-prefixes from the upstream feed when the downstream publishes.
A consumer's checklist: Ingest IP-Geo responsibly
If you consume IP geolocation for routing, risk, or compliance:
- Treat IP-geo as coarse: do not overfit decisions to city-level claims where the cost of error is high.
- Prefer authoritative signals where available (operator-published geofeeds) over purely inferred databases.
- Honor cache headers and refresh on schedule; if missing, poll conservatively (e.g., weekly at most).
- Fail closed on bad inputs (duplicate CIDRs, conflicting overlaps, invalid codes).
- Design for disputes and remediation: users will report errors; operationalizing corrections is part of a healthy pipeline.
Example: A minimal Geofeed row format
Below is a simple illustrative example of what "clean" entries look like conceptually (exact field requirements depend on the referenced geofeed specification). The key point is consistency: valid prefixes, standardized codes, and no duplicates.For a practical walkthrough on creating and publishing a geofeed, see our blog: IP Geofeed and How to Setup One?
ip_prefix,country_code,region,city,postal_code
203.0.113.0/24,PK,SD,Sukkur,65200
2604:6600:9a::/48,KR,KR-11,Seoul,Operationally, this is only useful if it is discoverable, refreshed, and conflict-free—otherwise it becomes another stale artifact.
Read the full position paper (PDF)
This blog post is a high-level translation of the full position paper:
IP Address Geolocation – Use Cases, Gaps, and Future Directions
In the paper, we go deeper on the ecosystem's predictable failure modes (coarse claims, leased-space conflicts, broken discovery, inconsistent refresh, weak authenticity) and propose pragmatic practices that can shift IP-geo from best-effort inference to a more dependable, privacy-respecting coarse signal.