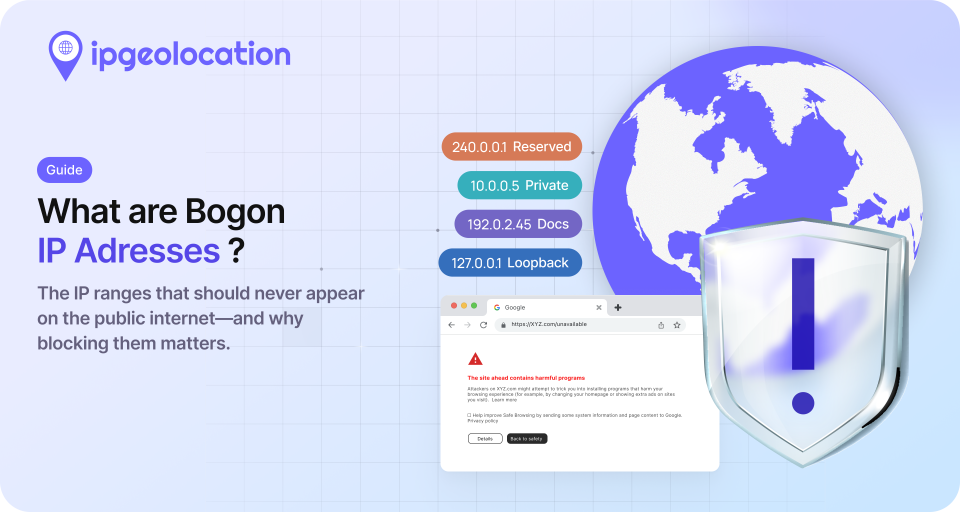
A bogon IP address is any IP address that has not been assigned to an entity by IANA (Internet Assigned Numbers Authority) or a Regional Internet Registry, or that has been reserved for special use by internet standards. These addresses should never appear as source or destination IPs in traffic crossing the public internet.
The term "bogon" comes from "bogus." It was coined in network engineering circles to describe IP space that has no legitimate reason to show up in routed traffic. If your firewall logs show packets from 192.0.2.45 or 240.0.0.1, something is wrong, because those addresses are not supposed to exist outside of documentation examples and reserved blocks.
Bogon addresses fall into two categories.
- The first is permanently reserved space: private ranges like 10.0.0.0/8, loopback addresses like 127.0.0.0/8, and other blocks set aside by RFCs for specific functions.
- The second is unallocated space: address blocks that IANA has not yet assigned to any RIR. This second category shrinks over time as new allocations happen, which is why bogon lists need regular updates.
TL;DR
- Bogon IP addresses are IPs not assigned by IANA/RIRs or reserved for special use (private networks, loopback, documentation, multicast)
- They should never appear in public internet traffic; their presence usually signals misconfiguration or spoofing
- Two types exist: permanently reserved (stable, defined by RFCs) and unallocated (shrinks as IANA assigns new blocks)
- Bogon filtering at router, firewall, and application layers is a baseline security practice
- IPv4 bogon space is now minimal due to exhaustion; IPv6 still has large unallocated ranges
- IP geolocation APIs like ipgeolocation.io reject bogon IPs since they have no real-world location data
For the full IPv4 and IPv6 bogon range tables, security implications, and filtering implementation details, keep reading.
Bogons vs. Martian Packets
These two terms get mixed up constantly, so it is worth being precise.
Martian packets are a specific subset of bogons. They carry source or destination addresses from ranges that are permanently reserved by RFC standards: private addresses (RFC 1918), loopback, link-local, documentation, and multicast ranges. The list of Martian ranges does not change unless an RFC is updated, which happens rarely.
Bogon addresses include all Martians plus any address space that is currently unallocated by IANA. In 2011, IANA distributed the last available IPv4 /8 blocks to the five RIRs, which means the "unallocated IPv4" portion of the bogon list is now nearly empty. For IPv6, the picture is different: roughly 85% of the IPv6 address space remains unallocated, making the IPv6 bogon list substantially larger.
The practical takeaway: Martian lists are static and easy to maintain. Full bogon lists require periodic updates to reflect new allocations.

Complete Bogon IP Address Ranges
The tables below list all bogon ranges as of April 2026. IPv4 bogon space consists almost entirely of reserved/special-use blocks, since nearly all allocatable IPv4 space has been distributed. IPv6 bogon space is larger because most of the address space remains unassigned.
1. IPv4 Bogon Ranges
| Netblock | Description |
|---|---|
| 0.0.0.0/8 | "This" network (current network identifier) |
| 10.0.0.0/8 | Private-use networks (RFC 1918) |
| 100.64.0.0/10 | Carrier-grade NAT (RFC 6598) |
| 127.0.0.0/8 | Loopback |
| 127.0.53.53 | Name collision occurrence |
| 169.254.0.0/16 | Link-local (RFC 3927) |
| 172.16.0.0/12 | Private-use networks (RFC 1918) |
| 192.0.0.0/24 | IETF protocol assignments |
| 192.0.2.0/24 | TEST-NET-1 (documentation, RFC 5737) |
| 192.168.0.0/16 | Private-use networks (RFC 1918) |
| 198.18.0.0/15 | Network interconnect device benchmark testing |
| 198.51.100.0/24 | TEST-NET-2 (documentation, RFC 5737) |
| 203.0.113.0/24 | TEST-NET-3 (documentation, RFC 5737) |
| 224.0.0.0/4 | Multicast |
| 240.0.0.0/4 | Reserved for future use |
| 255.255.255.255/32 | Limited broadcast |
There are 16 IPv4 bogon netblocks. The three RFC 1918 private ranges (10.0.0.0/8, 172.16.0.0/12, 192.168.0.0/16) are the most commonly seen in misrouted traffic because they are used in virtually every LAN.
2. IPv6 Bogon Ranges
| Netblock | Description |
|---|---|
| ::/128 | Node-scope unicast unspecified address |
| ::1/128 | Node-scope unicast loopback address |
| ::ffff:0:0/96 | IPv4-mapped addresses |
| ::/96 | IPv4-compatible addresses (deprecated) |
| 100::/64 | Remotely triggered black hole addresses |
| 2001:10::/28 | ORCHID (Overlay Routable Cryptographic Hash Identifiers) |
| 2001:db8::/32 | Documentation prefix |
| fc00::/7 | Unique local addresses (ULA) |
| fe80::/10 | Link-local unicast |
| fec0::/10 | Site-local unicast (deprecated) |
| ff00::/8 | Multicast (note: ff0e::/16 is global scope and may appear on the public internet) |
3. IPv6 6to4 and Teredo Bogon Ranges
Transition mechanisms like 6to4 and Teredo embed IPv4 addresses inside IPv6 addresses. When the embedded IPv4 address is itself a bogon, the resulting IPv6 address is also a bogon. These ranges are derived directly from the IPv4 bogon table above.
| Netblock | Description |
|---|---|
| 2002::/24 | 6to4 bogon (0.0.0.0/8) |
| 2002:a00::/24 | 6to4 bogon (10.0.0.0/8) |
| 2002:7f00::/24 | 6to4 bogon (127.0.0.0/8) |
| 2002:a9fe::/32 | 6to4 bogon (169.254.0.0/16) |
| 2002:ac10::/28 | 6to4 bogon (172.16.0.0/12) |
| 2002:c000::/40 | 6to4 bogon (192.0.0.0/24) |
| 2002:c000:200::/40 | 6to4 bogon (192.0.2.0/24) |
| 2002:c0a8::/32 | 6to4 bogon (192.168.0.0/16) |
| 2002:c612::/31 | 6to4 bogon (198.18.0.0/15) |
| 2002:c633:6400::/40 | 6to4 bogon (198.51.100.0/24) |
| 2002:cb00:7100::/40 | 6to4 bogon (203.0.113.0/24) |
| 2002:e000::/20 | 6to4 bogon (224.0.0.0/4) |
| 2002:f000::/20 | 6to4 bogon (240.0.0.0/4) |
| 2002:ffff:ffff::/48 | 6to4 bogon (255.255.255.255/32) |
| 2001::/40 | Teredo bogon (0.0.0.0/8) |
| 2001:0:a00::/40 | Teredo bogon (10.0.0.0/8) |
| 2001:0:7f00::/40 | Teredo bogon (127.0.0.0/8) |
| 2001:0:a9fe::/48 | Teredo bogon (169.254.0.0/16) |
| 2001:0:ac10::/44 | Teredo bogon (172.16.0.0/12) |
| 2001:0:c000::/56 | Teredo bogon (192.0.0.0/24) |
| 2001:0:c000:200::/56 | Teredo bogon (192.0.2.0/24) |
| 2001:0:c0a8::/48 | Teredo bogon (192.168.0.0/16) |
| 2001:0:c612::/47 | Teredo bogon (198.18.0.0/15) |
| 2001:0:c633:6400::/56 | Teredo bogon (198.51.100.0/24) |
| 2001:0:cb00:7100::/56 | Teredo bogon (203.0.113.0/24) |
| 2001:0:e000::/36 | Teredo bogon (224.0.0.0/4) |
| 2001:0:f000::/36 | Teredo bogon (240.0.0.0/4) |
| 2001:0:ffff:ffff::/64 | Teredo bogon (255.255.255.255/32) |
Why Bogon Traffic Is a Security Problem
Bogon source addresses in your logs are never innocent. Legitimate traffic does not originate from unallocated or reserved address space. When you see it, the explanation is either a network misconfiguration or deliberate spoofing, and the latter is far more common on public-facing infrastructure.
Attackers use bogon source addresses for a few specific reasons. Spoofed source IPs make it difficult to trace the origin of an attack, since the return path leads nowhere. DDoS amplification attacks frequently use bogon sources: the attacker sends requests to open resolvers with a spoofed source address, and the amplified responses flood the target. According to CAIDA's Spoofer Project, roughly 30% of autonomous systems still allow spoofed traffic to leave their networks, which means bogon-sourced packets remain a real problem in 2026.
Network scanning is another common use. Probing from bogon space lets an attacker map your open ports and services without exposing a traceable IP. If your intrusion detection system does not flag bogon sources, these scans blend into background noise.
On internal networks, bogon traffic in unexpected places often indicates a misconfigured device, a rogue DHCP server handing out private addresses on the wrong segment, or a VPN tunnel leaking internal routes. These are not security attacks, but they are still problems worth catching early.

How to Filter Bogon Traffic
Bogon filtering is considered a baseline security practice by organizations like MANRS (Mutually Agreed Norms for Routing Security) and is recommended in BCP 38 (RFC 2827). Filtering can happen at multiple layers, and most production networks implement it at more than one.
1. Router and Firewall ACLs
The most common approach is ingress filtering at your network edge. Configure access control lists on border routers or firewalls to drop any packet with a source address in the bogon ranges listed above. Egress filtering (blocking outbound traffic with bogon destinations) is equally important; it prevents your own network from leaking internal addresses or participating in spoofed-source attacks.
The key principle from BCP 38: if a packet arrives on an interface where that source address could not legitimately originate, drop it. This applies to bogon ranges and also to your own internal address space appearing on an external interface.
2. BGP Route Filtering
Network operators running BGP should filter bogon prefixes from their route tables. Accepting a bogon route advertisement for 10.0.0.0/8 or 192.168.0.0/16 would blackhole traffic destined for those ranges or, worse, create a path for traffic hijacking.
Team Cymru maintains a widely used Bogon Reference that provides regularly updated bogon prefix lists in formats compatible with major router platforms. The IANA IPv4 Address Space Registry is the authoritative source for current allocation status.
3. Application-Layer Bogon Detection
For developers building applications that process IP addresses, handling bogons at the application layer adds a useful validation step. If your application queries an IP geolocation API with a bogon address, no meaningful location data exists for that IP.
The ipgeolocation.io IP Geolocation API handles this explicitly. When a bogon IP is submitted, the API returns:
HTTP 423 Locked
{
"message": "'0.0.0.0' is a bogon IP address."
}
Bogon, private, and malformed IPs are not counted against your API quota, so validation checks do not consume credits. This makes it practical to use the API as a validation layer: submit the IP, check for a 423 response, and flag or discard the request before further processing.
This matters in real applications. If you are running ad verification, fraud scoring, or access control based on geolocation data, a bogon source IP is a strong signal that the request is either spoofed or coming from a misconfigured client. Catching it early saves processing time and prevents bad data from entering your pipeline.

Keeping Your Bogon Lists Current
Static bogon lists go stale. While the Martian/reserved ranges rarely change, the unallocated portion of the bogon list shifts every time IANA or an RIR makes a new assignment. For IPv4, this happens infrequently now that the free pool is exhausted. For IPv6, new allocations are still regular.
Recommended sources for up-to-date bogon data:
- IANA IPv4 Address Space Registry: The authoritative source for which /8 blocks are allocated, reserved, or available.
- Team Cymru Bogon Reference: Provides downloadable bogon prefix lists updated regularly. Supports BGP feed integration for automated updates.
- RIR delegation files: ARIN, RIPE, APNIC, LACNIC, and AFRINIC each publish daily delegation statistics showing which blocks they have assigned.
For production firewall and router filters, pulling updates at least daily is the recommended minimum. Some organizations subscribe to Team Cymru's BGP bogon feed, which pushes updates automatically as allocations change. This is the most reliable approach for networks where stale bogon filters could block newly legitimate traffic.
Frequently Asked Questions
A bogon is an IP address from space that is either reserved for special use or not yet allocated by IANA or a Regional Internet Registry. The term comes from "bogus" and was adopted by network engineers to describe any IP that should not appear in public internet routing tables. Bogon traffic on a public network indicates either misconfiguration or intentional spoofing.
Yes. Private addresses defined in RFC 1918 (10.0.0.0/8, 172.16.0.0/12, 192.168.0.0/16) are a subset of bogon addresses. They are valid for use on internal networks but should never appear as source or destination addresses in traffic crossing the public internet. If they do, it means something along the routing path is leaking internal addresses.
For the reserved/Martian portion, updates are rarely needed since those ranges are defined by RFCs that change infrequently. For the unallocated portion, daily updates are the recommended minimum for production network filters. IPv4 changes are now rare due to address exhaustion, but IPv6 allocations still happen regularly. Automated feeds from Team Cymru or RIR delegation files are the most reliable approach.
No. That is precisely why attackers use them. A bogon source address has no legitimate allocation, so there is no organization, ISP, or geographic location associated with it. Geolocation APIs will reject bogon lookups entirely because no real-world location data exists. Any packet with a bogon source address is effectively untraceable by design.
A well-built API rejects the request rather than returning empty or misleading results. For example, ipgeolocation.io's API returns HTTP 423 with a message identifying the IP as bogon. The lookup does not count against your API quota, so you can use it as a validation check without cost concerns.
Next Steps
If you are seeing bogon addresses in your traffic logs, start by implementing ingress filtering at your network edge. For application developers working with IP data, use your geolocation API's bogon detection to catch and discard these addresses before they reach your processing pipeline. The IP Security database from ipgeolocation.io can provide additional threat intelligence beyond bogon detection, including proxy, VPN, and Tor identification for IPs that are technically valid but still suspicious.